Even though you may not be a well-known company or brand, your company still needs to be concerned about security breaches.
In fact, it might surprise you to learn that the reality is quite the opposite: Attackers are aware that smaller businesses are most likely to be exposed.
Only 31% of the organizations surveyed for the government’s 2021 “Cyber Security Breaches Survey” had continuity plans for cyber security, and less than 15% had conducted an audit of their vulnerabilities.
It makes sense; according to Hemant Kumar, CEO and co-founder of Enpass, small firms “have less time and fewer resources to focus on cyber security, which typically takes a back-seat to sales-related activity.”
The potential gain is higher and the implications of a breach are more severe, but they also “typically have larger firms as clientele.”
When you consider that solutions are frequently viewed as “expensive and overcomplicated,” as stated by Pete Bowers, COO at NormCyber, it’s not all that unexpected that cyber security takes a backseat.
Although enterprise-level solutions can have enterprise-level price tags, Bowers writes, “small business owners would be advised to apply some simple free and affordable steps.”
It’s crucial to keep in mind that there is no such thing as “100% security,” and in the actual world of threat mitigation, there might be roadblocks.
You are still in a better position to decrease your risk if you know where to spend your resources.
Knowing which security gaps you have and which ones urgently need to be filled is the trick.
- Identification and verification
According to Tom Bridge, principal product manager at JumpCloud, identity is “usually the first issue that small organizations struggle with regarding security.”
For large companies, “there is a whole industry out there tackling identity and security utilizing strong authentication and single sign-on (SSO)”. This is the question of who is using a device and how you can prove it.
There is a caveat for smaller firms, though: “These systems frequently depend on Microsoft Active Directory, which is not intended for small businesses.”
You may close any vulnerabilities in your identification and authentication security by using the strength of password management, MFA, and the least privilege principle.
Given the prevalence of password reuse and the fact that many users choose one of the most popular passwords out of convenience, a simple password policy just won’t cut it.
Enforcing secure, one-of-a-kind passwords for all business-critical services and accounts is the straightforward solution.
According to John Goodacre, director of the UK Research and Innovation “digital security by design” challenge and professor of computer architectures at Manchester University, “Random password generators are a great option for guaranteed one-time use, with password managers helping users to stay on top of these.”
Any identity management policy that is possible should also incorporate a strong MFA mechanism.
According to Lee Wrall, director at managed services provider (MSP) Everything Tech, a recent Microsoft study found that 99.9% of the cyberattacks that their clients reported could have been avoided if MFA had been enabled.
It’s time to look for another vendor, advises Wrall, if the first doesn’t provide help. In all honesty, it’s not hard to locate vendors who see the significance of MFA as a selling point.
“According to Adam Seamons, systems and security engineer at GRC International Group, “the technology of MFA has been employed in the banking business for a long time and is now present in many mainstream products like Microsoft Office 365, Google Workspace, and Apple iWork.
While enabling MFA won’t prevent account penetration, it will make things much more difficult for attackers.”
That takes us to the last line of defense in identity security: the principle of least privilege, which basically means making sure that only those who need access to data and systems may get it.
“If everyone in your organization has access to critical data and can modify systems, then all it takes is one account to be infected by malware or a cyberthief to end it all,” says Seamons.
Putting your thumb on the security side of the scale is rarely a terrible idea because, unavoidably, employees in the small business environment frequently have to wear numerous hats and operate across a variety of jobs and systems. As a result, you may need to measure convenience against security.
2.Patch control & Removal
According to Jamie Akhtar, CEO and co-founder of CyberSmart, patching is the security flaw that most small businesses need to solve right away.
Even the best software eventually becomes old, has a breach, or develops flaws, according to him.
The issue is that the amount of customers that routinely update their operating systems and software determines how effective patching is. For smaller businesses, this can be challenging to manage.
The procedure can be centralised with the use of patch management tools, but the true challenge is developing a patching routine.
“Misconfigured, outdated, and unpatched software are three key weaknesses that hackers aim to attack,” explains Ken Galvin, senior product manager at Quest.
Smaller companies without an IT department will benefit the most from being able to automate the process.
He advises users to “look for products with built-in vulnerability scanning, which can discover vulnerable devices and tell you how to fix issues.”
- Phishing and email
Even because email is so essential to almost every business, it may seem strange to consider it a security flaw, but it is.
According to Galvin, “A business email system is an open front door that accepts almost any message submitted to a genuine email account.”
Even if you remove risky attachments, phishing attacks continue to be a problem that is nearly hard for you to control.
Your staff will have a big impact on how well you are able to thwart these tactics, says Galvin.
Yes, security education, email screening, and antivirus software all help reduce the basics.
However, he advises “greater visibility and control of the devices that access your network, through products like unified endpoint management software,” for better protection.
For a small business, that might be a significant ask and expenditure.
Nevertheless, attackers have a lot of access to various points of entry to your platforms and services, thus it is crucial to invest in their security.
- How to combat the development of phishing as a service (PhaaS)
If a member of your staff does fall prey to a phishing attempt, keep in mind that your response may still have an effect on the entire danger landscape.
Goodacre urges small businesses to always disclose phishing attacks to Action Fraud and to avoid punishing staff members for doing so because it deters them from reporting such events in the future.
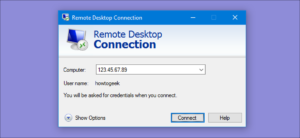
- Remote desktop
The use of RDP and other remote-access tools has multiplied in recent years as firms have embraced hybrid business models more and more.
However, there is a risk: “With this window into your business environment,” warns Galvin, “if hackers are successful in locating open ports by using penetration testing software like Cobalt Strike, a brute force password hack on those open ports to gain access could be implemented, ultimately leading to a complete IT system control takeover.”
Ioan Peters, co-practice leader for EMEA cyber risk at Kroll, advises that you should only use a virtual private network (VPN) or virtual desktop solution to access your remote desktop in order to reduce the likelihood that an attacker will find a way in and, to the greatest extent possible, to create a barrier between employee personal systems and business-critical resources.
5. The Cloud
Tim Mackey, lead security strategist at the Synopsys Cybersecurity Research Center, asserts that in 2022, the security of a small firm will depend on how strong its cloud service providers are.
In reality, one of the biggest problems for any size firm is preventing sensitive data from being taken out of the system by unauthorized individuals.
This cyber fissure threatens to develop into a full-blown security sinkhole as businesses become more dependent on cloud-based services like Google Workspace and Microsoft Office 365 to empower their staff.
Burak Agca, a security engineer at Lookout, says that while small businesses might not have an in-house security team, data protection can be aligned with secure IT practices regarding how users access the infrastructure and the data therein. Lee Wrall advises you to seriously consider investing in a managed service provider: “The longer you ‘wing’ your IT on your own, the more you’ll be at risk,” he warns.
- Untrusted applications
Small businesses frequently lack the capacity to thoroughly analyze everything for security flaws, which can result in dangerous software being accidentally installed on your company network.
Since users could unintentionally download programs that are riddled with malicious loaders that drag malware down to the device after installation, Agca notes that this mostly pertains to mobile apps. These are only a few considerations when it comes to the security of your small business.
For your business, Preferred Computer Solutions can set into action a plan that will assist and help to protect you from harm and hackers.





Recent Comments